SVG images – the hidden threat your anti-virus can’t see
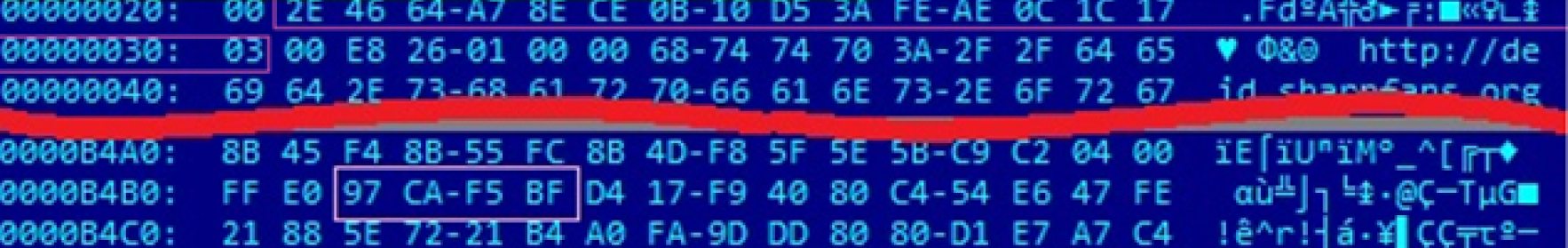
A new type of file-based attack is spreading quickly, cleverly circumventing standard detection-based protections. This method of attack employes malicious emails with HTML attachments that include embedded, base64-encoded, SVG images. SVG images can, by design, include Javascript tags, and these script tags are now being abused by attackers to smuggle JavaScript into HTML files.
Most web browsers will decode and execute the embedded JavaScript as if it were a standard part of the document’s HTML. Since the malware payload is being constructed directly on the victim computer and not being delivered through a network transmission most anti-malware tools designed to filter malicious content in transit are ineffective.
In one case (Quakbot), the JavaScript that was smuggled inside of the SVG image contained the entire malicious zip archive. When the victim opened the HTML attachment from the email the smuggled JavaScript code inside the SVG image created a malicious zip archive, and then presented the user with a dialog box to decrypt and save the file.
This new type of file-based attack poses a considerable challenge for detection-based security tools. CDR-based security solutions, however, retain the upper hand. Content Disarm and Reconstruction (CDR) file sanitization technology disarms all malicious embedded elements, including any hidden scripts or heavily obfuscated archives, through recursive unpacking and scanning, followed by detection-less threat mitigation, through reconstruction. In tests run recently at Sasa Software’s cybersecurity research lab, all malicious scripts that were included in embedded SVG images and sent through GateScanner’s CDR engines were completely disabled, and the threats were neutralized.
Keywords: SVG image, Quakbot, Malware, Anti-malware, Content disarm and reconstruction, CDR, Smuggled HTML